GrayShift – USA Atlanta-based Startup.
GrayKey – Hardware(gadget)/Tools with Software Services of GrayShift to unlock (passcode) iPhones.
After the connection of iphone, the GrayKey install one sw to disable the Security Enclave and hacking the passcode using brute force.
Tips: For your own security, use very long passcode or use/upgrade to iOS 12.
30s used to find one passcode with 6 digits.

Note:
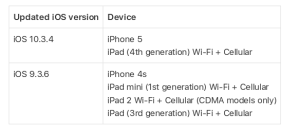
iPhone with iOS 12, no longer break the passcodes of any iPhone running iOS 12 or above.
on iOS 12, GrayKey can do:
draw out unencrypted files, such like file sizes and folder structures.
Other Tips for iPhone Protection
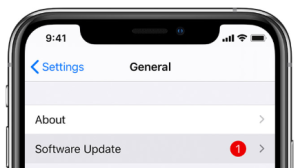
Erase iPhone after 10 failed attempts
To set iPhone to erase all data after 10 failed passcode attempts.
Go to Settings > Touch ID & Passcode, scroll down to the bottom and enable the option “Erase Data”.